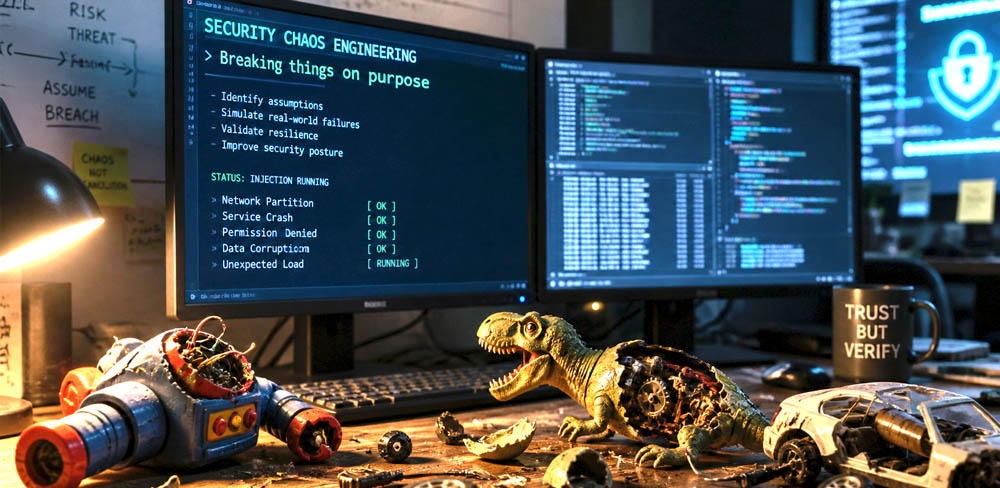
Cybersecurity Strategy: Breaking Things on Purpose - Security Chaos Engineering
As kids, we were basically tiny demolition experts with no formal training. We broke toys, snapped bike chains, shattered lamps, and occasionally our own bones. Sometimes by accident, and sometimes for fun to see what would happen. And every adult in the room would scream at us, “HOW COULD YOU DO THAT!!”, and then sigh and say something like, “Well… at least they’re learning.”
Then we grow up and pretend we’ve evolved past all that. We convince ourselves that maturity means not breaking things anymore - that life is now about stability, predictability, and keeping all the metaphorical lamps intact.
But what if that childhood instinct wasn’t chaos… but practice?
What if breaking things - carefully, intentionally, and with adult supervision - is still one of the smartest strategies we have?
Because in the world of modern systems and cybersecurity, the real danger isn’t the mess you make on purpose. It’s the mess you never see coming.
When “Oops” Becomes a Strategy
In most organizations, breaking something in production is the fastest way to get everyone’s attention - and possibly a meeting with leadership that no one enjoys. Stability is prized, uptime is celebrated, and incidents are treated like rare and unfortunate accidents.
So the idea of intentionally breaking systems might sound like a terrible plan.
It is a bit like stress-testing a bridge by driving increasingly heavier trucks over it while hoping for the best. Except in cybersecurity, the trucks are already coming - and they are not asking for permission.
Attackers do not wait for convenient timing. They probe systems constantly, looking for weak points, misconfigurations, and overlooked vulnerabilities. The uncomfortable reality is that most organizations only discover their weaknesses after someone else does.
This is where Security Chaos Engineering offers a different approach. Instead of waiting for failure, teams simulate it. They introduce controlled disruptions, mimic attack scenarios, and observe how systems - and people - respond.
The goal is not to cause damage. It is to gain clarity.
Because in modern, distributed environments, the most dangerous vulnerabilities are often the ones that remain hidden until they are exploited.
What Is Security Chaos Engineering?
Extending Chaos Engineering into Security
Chaos engineering began as a way to improve system reliability by intentionally introducing failures. The same principles can be applied to cybersecurity, creating a proactive method for testing defenses.
Security chaos engineering focuses on simulating real-world attack scenarios in controlled environments. These simulations help organizations understand how their systems behave under stress and whether their defenses are truly effective.
Rather than asking whether a system is secure, the approach asks a more practical question: what happens when it is not?
How It Differs from Traditional Security Testing
Most organizations already use tools such as vulnerability scanners and penetration tests. While valuable, these methods have limitations. They are often periodic, limited in scope, and conducted in controlled environments that may not reflect real-world conditions.
Security chaos engineering addresses these gaps by introducing continuous, real-time testing within operational systems. It evaluates not only whether vulnerabilities exist, but also how quickly they are detected and resolved.
This shift transforms security from a static checklist into a dynamic, ongoing process.
Core Principles of Security Chaos Engineering
Assume Breach as a Starting Point
A key principle in modern cybersecurity is the assumption that breaches are inevitable. Security chaos engineering embraces this mindset by designing experiments that simulate compromised systems or unauthorized access.
This approach encourages teams to focus on detection, containment, and recovery rather than relying solely on prevention.
Controlled Experiments in Real Environments
Testing security in isolated environments can miss critical interactions and dependencies. Security chaos experiments are designed to run in production or production-like settings, where systems behave as they would under real conditions.
These experiments are carefully controlled to minimize risk, with safeguards in place to prevent unintended consequences.
Measurement and Continuous Improvement
Every experiment is tied to measurable outcomes. Organizations evaluate how quickly threats are detected, how effectively alerts are triggered, and how efficiently teams respond.
Over time, these insights drive continuous improvement, strengthening both technical defenses and operational processes.
Types of Security Chaos Experiments
Security chaos engineering encompasses a range of experiment types, each targeting different aspects of a system’s security posture.
Identity and Access Simulations
Identity systems are a common target for attackers. Experiments in this area focus on testing how systems respond to unauthorized access attempts or privilege escalation.
Typical scenarios include:
- Simulating compromised credentials
- Testing access to restricted resources
- Introducing misconfigured permissions
These experiments help validate whether access controls are enforced and whether suspicious activity is detected promptly.
API and Network-Level Attacks
APIs and network interfaces are critical entry points for modern applications. Security chaos experiments can simulate abnormal traffic patterns, malformed requests, or attempts to bypass rate limits.
The objective is to ensure that systems can handle unexpected behavior without exposing vulnerabilities or degrading performance.
Data Exfiltration Scenarios
Protecting sensitive data is a top priority for most organizations. Chaos experiments in this category simulate attempts to access or transfer data in unauthorized ways.
These scenarios test whether monitoring systems can detect unusual data movement and whether safeguards prevent unauthorized access.
Incident Response Drills
Security is not just about technology; it is also about people and processes. Incident response experiments evaluate how teams react to simulated threats.
These drills provide insight into communication, escalation procedures, and decision-making under pressure.
The Role of Observability in Security Chaos Engineering
Visibility as a Foundation
Security chaos engineering relies heavily on observability. Without clear visibility into system behavior, it is impossible to evaluate the impact of experiments.
Logs, metrics, and traces provide the data needed to understand how systems respond to simulated attacks.
Correlating Signals Across Systems
In distributed architectures, security events often span multiple components. Observability enables teams to correlate data across services, creating a cohesive view of system activity.
This holistic perspective is essential for identifying root causes and understanding the full impact of security events.
Benefits of Security Chaos Engineering
Revealing Hidden Weaknesses
Some vulnerabilities only appear under specific conditions. By introducing controlled disruptions, organizations can uncover issues that would otherwise remain undetected.
Improving Detection and Response
Simulated attacks provide valuable training opportunities for security teams. Over time, this leads to faster detection, more accurate alerts, and more effective incident response.
Strengthening Overall Security Posture
Continuous testing ensures that security measures evolve alongside systems. Organizations can validate their defenses regularly and adapt to emerging threats.
Aligning Security with Business Risk
Security chaos engineering helps translate technical findings into business impact. This allows leaders to prioritize investments and make informed decisions about risk management.
Challenges and Considerations
Now here is where you have to be careful, it is one thing to decide to do Security Chaos Engineering, but it is another thing to successfully implement it. Here are things you need to line up before you commit to applying it to a project:
Managing Risk Carefully
Even controlled failure isn’t something you just “try and see what happens.” It requires intention, boundaries, and a healthy respect for the blast radius.
- Define clear limits - Establish what can be disrupted, when, and under what conditions.
- Put safeguards in place - Use monitoring, rollback plans, and isolation to prevent cascading issues.
- Assess impact continuously - Treat every experiment as data, not chaos.
Example:
A team testing their incident‑response workflow might simulate a database outage only in a staging environment with automated rollback enabled. This lets them observe how alerts fire, how quickly teams respond, and where communication breaks down - without risking customer‑facing systems.
Gaining Organizational Support
Intentionally breaking things can sound reckless until people understand the purpose behind it.
- Explain the “why” clearly - Frame it as proactive risk reduction, not random destruction.
- Show early wins - Demonstrate how small experiments uncover hidden vulnerabilities.
- Align with business goals - Connect resilience testing to uptime, customer trust, and reduced incident costs.
Example:
A security team might run a small-scale phishing simulation and show leadership how many employees clicked the bait. The data makes the value obvious: controlled failure today prevents uncontrolled disaster tomorrow.
Tooling and Expertise
Chaos engineering isn’t a hobby project - it needs the right tools and people.
- Invest in specialized platforms - Tools that safely inject faults, track impact, and automate experiments.
- Build internal expertise - Train engineers to design, run, and interpret experiments responsibly.
- Integrate with existing workflows - Ensure experiments fit into CI/CD, monitoring, and incident‑response processes.
Example:
An organization might adopt a chaos‑testing platform that can simulate API latency. Engineers learn to run latency injections during off‑peak hours, observe how services degrade, and adjust autoscaling rules accordingly - turning controlled stress into stronger architecture.
Best Practices for Implementation
Getting started with security chaos engineering doesn’t require dramatic experiments. The goal is to build confidence, gather insights, and strengthen systems step by step.
Start with Low-Impact Experiments
- Begin small - Use scenarios that won’t disrupt critical services.
- Build confidence gradually - Let teams practice in safe, predictable environments.
- Refine processes early - Use low‑risk tests to tune communication and workflows.
Example:
A team might start by simulating mild API latency in a non‑critical service. This helps them validate monitoring alerts and response playbooks without risking customer‑facing functionality.
Define Clear Objectives
- Set a specific goal - Know exactly what you’re testing: detection, response, resilience, or communication.
- Make results actionable - Tie each experiment to measurable outcomes.
- Avoid “chaos for chaos’ sake” - Every test should answer a meaningful question.
Example:
An experiment might focus solely on whether an intrusion detection system flags a simulated credential‑stuffing attempt within a target time window.
Integrate with Existing Security Programs
- Complement - not replace - current practices - Chaos engineering enhances penetration testing, red teaming, and threat modeling.
- Create a unified strategy - Use findings to strengthen your broader security posture.
- Share insights across teams - Ensure learnings feed into architecture, operations, and compliance.
Example:
After a chaos experiment reveals a blind spot in log correlation, the security team updates their threat‑modeling assumptions and adjusts pen‑test scenarios accordingly.
Foster a Culture of Learning
- Focus on improvement, not blame - Experiments should reveal weaknesses, not create scapegoats.
- Encourage cross‑team collaboration - Security, engineering, and operations should learn together.
- Normalize curiosity - Treat every finding as a chance to build resilience.
Example:
When a simulated outage exposes a misconfigured alert rule, the team reviews it openly in a blameless post‑experiment session, updates the rule, and documents the fix for future onboarding.
Real-World Scenario: A Controlled Breach Simulation
Consider a financial services company operating a cloud-native application. The security team decides to simulate a compromised API key with elevated permissions.
During the experiment, the system allows access to sensitive endpoints without triggering immediate alerts. Logs capture the activity, but alerts are delayed due to high noise levels. The incident response team takes longer than expected to escalate the issue.
Based on these findings, the organization implements several improvements. Access controls are tightened, alert thresholds are adjusted, and response procedures are updated.
The result is a measurable increase in detection speed and response effectiveness, reducing the organization’s overall risk exposure.
The Future of Security Chaos Engineering
Continuous Security Validation
Security is moving toward continuous validation rather than periodic assessment. Chaos engineering supports this shift by enabling ongoing testing and improvement.
Integration with AI and Automation
AI technologies are enhancing chaos engineering by identifying high-risk scenarios, automating experiments, and analyzing results at scale. This makes testing more efficient and effective.
Security as a Strategic Advantage
Organizations that proactively test their defenses gain a competitive edge. Strong security builds trust, supports compliance, and enables innovation.
Conclusion: Break It Before Someone Else Does
In an environment where cyber threats are constant and evolving, waiting for an attack to reveal weaknesses is no longer a viable strategy. Security chaos engineering offers a proactive approach, allowing organizations to simulate threats, test defenses, and strengthen resilience.
By combining controlled experimentation with strong observability and continuous improvement, teams can uncover hidden vulnerabilities and improve their ability to respond to real incidents.
The takeaway is clear: the most secure systems are not those that never fail, but those that are designed to handle failure effectively.
For organizations ready to take the next step, the path forward is straightforward. Start small, define clear objectives, and integrate chaos engineering into existing security practices.
Because in cybersecurity, breaking things on purpose may be the smartest way to keep everything running.
For any questions about Security Chaos Engineering in Modern Cybersecurity, please contact us at ScreamingBox.
For more info on some of the topics in this blog, check out our podcast on AI, Security & Software Governance